Operational AI for the Real World
A command-line tool that makes managing physical equipment completely predictable for both people and AI agents.
A Common Language for Humans and AI
Xyte CLI acts as a common language so that human technicians and AI assistants can work together reliably, ensuring equipment reacts exactly the same way every time.
While the Xyte portal remains the primary interface for everyday use, the CLI is a power tool designed for managing large device estates through repeatable automation.

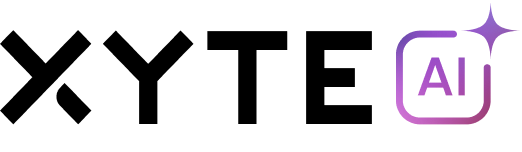
AI Readiness & the Skills Bootstrap
Xyte CLI is AI-native at the interface level — it doesn't force AI agents to "click" through a website like a human. Through the Skills Bootstrap, a single command installs pre-built instructions that teach AI agents exactly how to interact with the environment.
Schema-validated JSON outputs ensure that machine-readable data is always structured and easy for software to act upon without errors.
Guarded Writes & Human-in-the-Loop
Managing physical infrastructure requires strict safety controls. Xyte CLI uses guarded writes — sensitive actions like rebooting a device or changing a configuration require explicit human confirmation before execution.
This "human-in-the-loop" model allows AI to plan a solution while ensuring a person remains the final gatekeeper for any real-world changes.
Explicit Confirmation
Every sensitive write action requires human approval before execution.
Full Auditability
Every action is logged and traceable for compliance and review.
AI Plans, Humans Approve
AI agents can draft solutions, but a person is always the final gatekeeper.
Use Cases
Schedule consistent snapshots across thousands of endpoints to automatically flag unusual behavior and generate daily summaries — keeping your entire device fleet healthy without manual checks.
Pull deep-dive system data on demand to create standardized reports that are ready for human or machine review — accelerating root cause analysis across your infrastructure.
Execute approved device actions through auditable and repeatable workflows — ensuring every remediation step is documented, safe, and consistent across your fleet.